The Unit of Authority
Why governance requires a first-class primitive, not a policy layer
Editor’s note: This essay opens Phase III of the series. Where the preceding articles dismantled inadequate models of control; hierarchy, human-in-the-loop, oversight-as-governance, this article names what must replace them: authority as a first-class architectural primitive. What follows is not a role description or a policy recommendation. It is a structural claim.
Every system that acts autonomously exercises authority.
It may not call it authority. It may call it a default, a fallback, a routing decision, a threshold. But structurally, the effect is the same: a component of the system determines what happens next, and the rest of the system proceeds as if that determination were legitimate.
This is the condition the previous articles have been converging on.
Hierarchy collapsed, not because leaders failed, but because decision velocity outgrew the structures designed to contain it. Human-in-the-loop did not restore control; it introduced latency into systems whose defining property is speed. Oversight became retrospective. Governance became narrative. And through it all, decisions continued to be made; faster, more distributed, less visible, by components that were never explicitly granted the right to make them.
Authority was exercised.
It was never designed.
That gap, between authority exercised and authority designed, is where instability originates. Not in the intelligence of agents. Not in the speed of execution. In the absence of an explicit, enforceable unit of authority that can be granted, scoped, constrained, delegated, observed, and revoked.
This article introduces that unit.
What authority is not
Authority is frequently conflated with adjacent concepts. These conflations are not semantic. They are architectural. Each one leads to a different failure mode.
Authority is not a role: Roles describe what a component is. Authority defines what a component is allowed to decide. A fraud agent and a payment agent may occupy different roles, but if both can independently authorise a transaction, they hold overlapping authority, and the system has no mechanism to resolve the conflict. The failure in that scenario is not cognitive. It is constitutional.
Authority is not a permission: Permissions govern access to resources: read, write, execute. Authority governs the right to determine outcomes. A component may have permission to call an API but no authority to decide whether the call should be made. Permissions are necessary infrastructure. They are not sufficient governance.
Authority is not a policy: Policies express intent. They describe what should happen, under what conditions, according to whom. But policies are declarative. They do not enforce themselves. A policy that is not embedded in architecture is an aspiration. Authority, as a primitive, must be enforceable at the point of action, not merely referenced during review.
Authority is not intelligence: A capable model does not become authoritative by virtue of its capability. The capacity to reason well does not confer the right to decide. In autonomous systems, intelligence and authority must be separated deliberately, because conflating them produces the most dangerous failure mode of all: a system that can act competently outside the bounds of what it was ever permitted to do.
Authority as a first-class primitive
If authority is not a role, a permission, a policy, or a capability... then what is it?
Authority is a decision right.
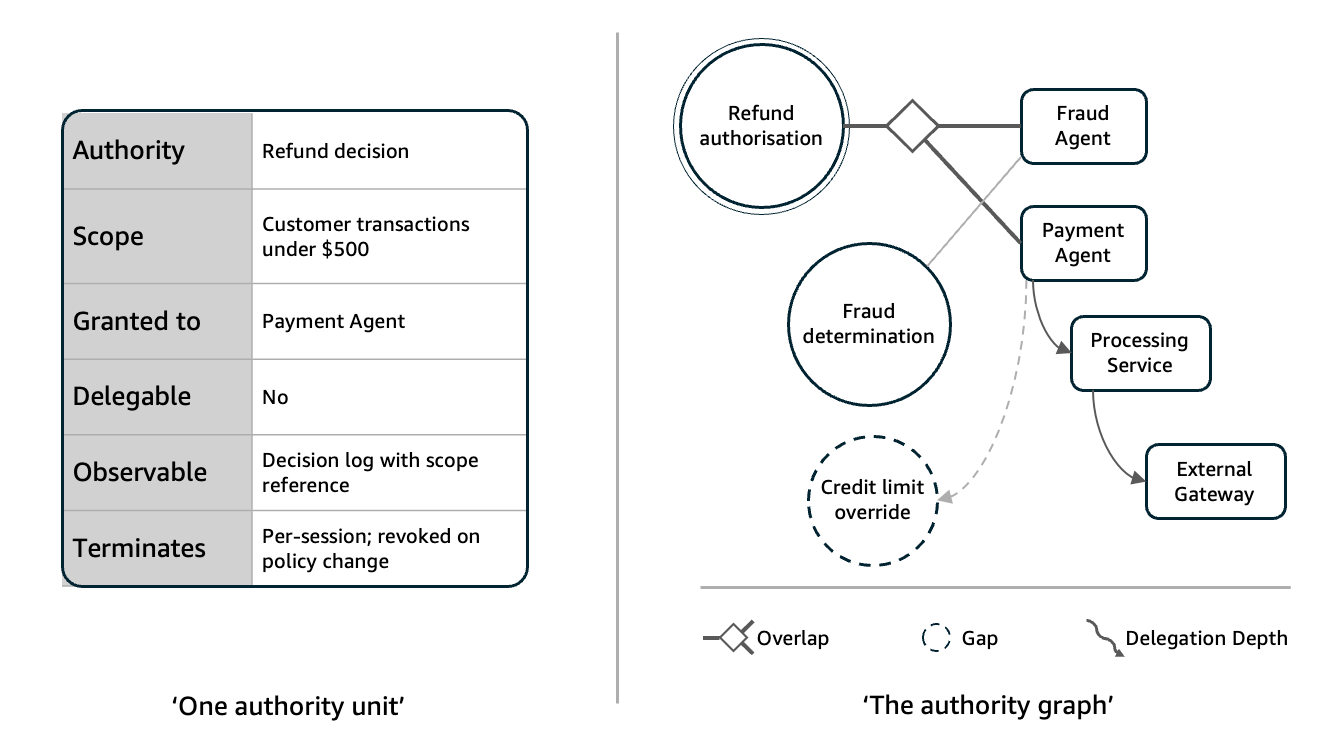
More precisely: authority is the explicit, scoped, enforceable right of a system component to determine an outcome within defined boundaries, subject to delegation rules, observability requirements, and termination conditions.
This is not a metaphor. It is a structural definition. And each element of it carries architectural weight.
Explicit means authority is not inferred, assumed, or inherited by default. If a component exercises authority that was never granted, the system is ungoverned at that point, regardless of whether the decision was correct.
Scoped means authority has boundaries. A decision right that applies everywhere applies nowhere meaningfully. Scope defines the domain of action: what kinds of decisions, over what inputs, within what context, up to what consequences. Without scope, authority is indistinguishable from unconstrained autonomy.
Enforceable means the system can prevent action that exceeds granted authority. Enforcement is not monitoring. Monitoring detects violations after they occur. Enforcement prevents them before execution completes. A system that can only detect authority violations is descriptive. A system that can prevent them is governed.
Subject to delegation rules means authority can be passed from one component to another, but only under conditions that are themselves explicit and enforceable. Delegation without rules is abdication. The delegating component must define what is being delegated, to whom, under what constraints, and whether the delegate may further delegate. Authority that flows without these rules degrades into implicit autonomy, which is where the series began.
Observable means the exercise of authority produces a legible record: not merely of what happened, but of what authority was invoked, by which component, under what scope, and whether that exercise remained within bounds. Without observability, authority cannot be audited, and governance becomes forensic rather than structural.
Subject to termination conditions means authority has an end. It expires, it is revoked, it lapses when conditions change. Authority that cannot be withdrawn is sovereignty, and sovereignty within a governed system is a contradiction. Every unit of authority must carry conditions under which it ceases to apply.
The authority graph
When authority is defined as a primitive, the relationships between authorities become a structure: the authority graph.
This is not an org chart. It is not a dependency graph. It is not a call graph. It is a map of decision rights; who holds them, under what scope, with what delegation chains, and where conflicts between them must be resolved.
The authority graph makes three things visible that are typically hidden in autonomous systems.
First, overlap. When two components hold authority over the same decision space, the graph reveals it. In the absence of an authority graph, overlap is discovered at runtime, usually as a conflict, often after consequences have propagated.
Consider a system in which a customer submits a refund request. An LLM interprets the intent and routes it to a payment agent, which issues the refund. In parallel, a fraud agent evaluates the same transaction and flags it. Both agents acted correctly within their own scope. Both exercised authority. But the system had no mechanism to determine whose authority governed the outcome. The refund was issued. The fraud flag was raised. No arbitration existed between them.
The failure was not intelligence. Both agents reasoned well. The failure was constitutional: two legitimate authorities overlapped, and the system had no designed resolution. The authority graph does not prevent overlap. It makes overlap explicit, so that arbitration can be designed rather than improvised.
Second, gaps. When no component holds authority over a decision that the system must make, the graph reveals the absence. Gaps are more dangerous than overlaps, because they are silent. A system with an authority gap does not fail visibly, it acts without governance, and the absence of authority is discovered only when someone asks who was responsible for a decision that no one was explicitly permitted to make.
Third, depth. Delegation chains create depth in the authority graph. A supervisor delegates to an agent. The agent delegates a subtask to a specialised tool. Each link in the chain is a point where authority may be diluted, transformed, or lost. When delegation depth is untracked, the system cannot answer a basic governance question: under whose authority did this action ultimately occur? The authority graph preserves provenance, not of data, but of the right to decide.
Why this is a constitutional claim
The language is deliberate.
Constitutions do not describe behaviour. They define what is permissible. They establish the conditions under which power may be exercised, and the limits beyond which it may not. They are prior to action, not derived from it.
The unit of authority serves the same function in autonomous systems.
It is not a runtime feature. It is not an observability enhancement. It is a constitutional layer: a set of structural commitments about who may decide what, under what conditions, and what happens when those conditions are violated.
Without this layer, every other mechanism; monitoring, audit, review, escalation, operates in a vacuum. They can observe behaviour, but they cannot evaluate it against a defined allocation of rights. They can detect anomalies, but they cannot determine whether an action was authorised or merely successful.
This is the distinction that separates governed systems from systems that merely appear governed.
A system that produces correct outcomes is functional.
A system that produces correct outcomes within explicitly granted authority is governed.
A system that produces correct outcomes outside its authority is dangerous, because it has demonstrated that governance is bypassable, and the next incorrect outcome will have no structural defence.
What changes when authority is explicit
Three shifts follow immediately.
Accountability becomes structural, not narrative. When authority is explicit, the question “who was responsible?” has a designed answer. Responsibility traces back to granted authority, not to whoever happened to be nearest the failure. Post-incident reviews shift from blame allocation to authority analysis: was the authority correctly scoped? Was delegation appropriate? Were termination conditions met? These are engineering questions, not organisational politics.
Conflict becomes designable. Overlapping authority is no longer a surprise discovered at runtime. It is a structural property that can be identified during design and resolved through arbitration. The authority graph does not eliminate conflict, it makes conflict a first-class design concern, with explicit resolution mechanisms rather than ad hoc escalation.
Delegation becomes auditable. Every transfer of authority; from supervisor to agent, from agent to tool, from system to external service, carries explicit terms. The chain of delegation is traceable, and at any point the system can answer: under whose authority is this component acting, and have the conditions of that delegation been satisfied? This is the foundation on which trust is built, not as a sentiment, but as a verifiable property.
The obligation this introduces
Naming authority as a primitive is not a simplification. It is an obligation.
It means that every component in an autonomous system must have an explicit answer to four questions:
What decisions am I authorised to make?
Under what conditions does that authority apply?
Who granted this authority, and may I delegate it?
Under what conditions does this authority expire or get revoked?
If any component cannot answer these questions, it is ungoverned. It may still function. It may still produce correct outputs. But it operates outside the constitutional layer, and any system that tolerates ungoverned components has already accepted that governance is optional.
Governance is not optional if autonomy is structural.
And autonomy, as this series has established, has been structural for longer than we have been willing to admit.
What comes next
This article has introduced authority as a first-class architectural primitive: explicit, scoped, enforceable, delegable, observable, and terminable. The authority graph has been named as the structure through which these units of authority relate, conflict, and compose.
But a primitive alone does not govern.
Authority units must compose. Supervisory domains must interoperate. Delegation chains must cross boundaries without losing coherence. What happens when two authority graphs meet, when independently governed systems must coordinate, is where the primitive is tested.
The next article examines composition: how units of authority combine, how delegation scales across domains, and why the authority graph must be composable if autonomous systems are to remain governed beyond the boundary of a single design.
Autonomy was already here.
Hierarchy could not govern it.
Human-in-the-loop could not restore it.
Oversight could not contain it.
Authority; designed, explicit, and enforceable, is how governance begins.
Next in the series: Composing Authority


