Governance at Machine Speed
Constraint precedes cognition. This is not a principle. It is an engineering requirement.
Constraint precedes cognition.
Authority has been designed: explicit, scoped, enforceable. It composes across boundaries through contracts defined before the interaction begins. It is legible: attributable, traceable, interpretable, verifiable. The constitutional architecture exists.
But legible to whom? And at what speed?
A human reading a legibility record after the fact is performing audit. A human reading it in real time is performing oversight. Neither scales to the speed at which autonomous systems operate. Decisions propagate in milliseconds. Authority composes across boundaries faster than any human can review. The legibility record exists, but by the time a human reads it, the system has already acted, composed, and moved on.
The constitutional architecture built in the previous three articles defines what governance must contain. It does not yet address when governance must operate. Governance that follows action; that reviews, monitors, approves, or audits after the decision has been made; is governance that has already lost. The answer is not faster humans. It is governance encoded ahead of cognition.
The speed problem is not about faster humans
Three compensations present themselves. Each fails for the same structural reason.
Faster review. More reviewers, shorter queues, faster approval cycles. This scales linearly with transaction volume. At machine speed, even millisecond-scale human review introduces latency that exceeds the system’s decision cycle. The series dismantled this in Phase I: human review degrades under volume. Decision volume grows faster than any review capacity. Context collapses under throughput. Review shifts from understanding to pattern matching. Scaling oversight does not scale governance. It scales the artefacts of governance while the substance leaks out.
Sampling and audit. Review a statistical sample. Accept that most decisions proceed unreviewed. Audit after the fact. This is monitoring, it discovers governance failures after they occur. At machine speed, the gap between action and audit widens until remediation becomes the primary governance activity. The system acts. Audit discovers what it did. Remediation restores order. This is crisis management with a governance label. It is not governance.
Automated review. Replace the human reviewer with an AI reviewer. The system evaluates its own decisions. This is the most dangerous compensation, because it collapses the distinction between the governed entity and the governance mechanism. If the agent evaluates its own boundaries, governance has not been automated. It has been absorbed into the cognitive process it was meant to constrain.
This is where the distinction between training-based governance and enforcement-based governance becomes structural. Constitutional AI trains models to follow principles, producing a statistical disposition to comply. The model is more likely to follow the principles. It is not structurally prevented from violating them. Disposition can drift, degrade, or be circumvented by adversarial input. A system that governs through disposition is a system that hopes governance holds. A system that governs through enforcement is a system that has made governance structural.
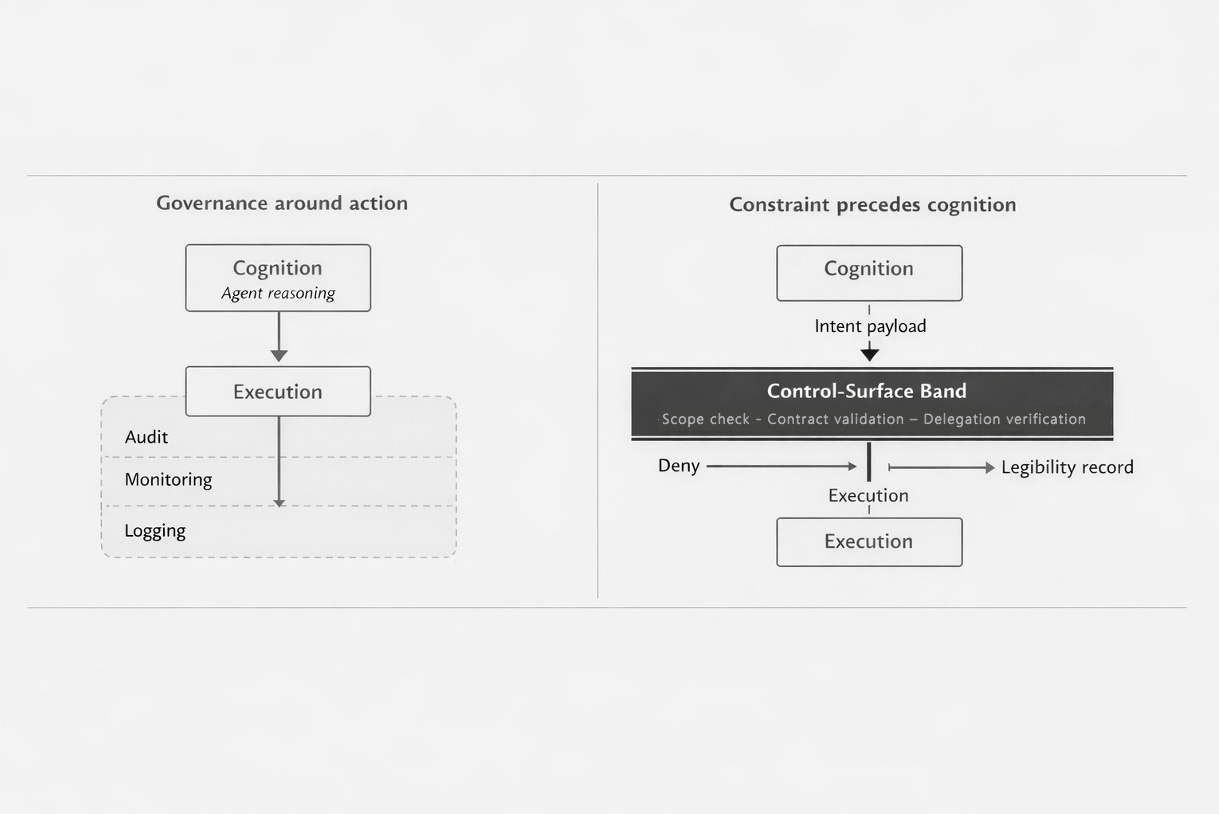
Each compensation fails for the same reason: it applies governance around action rather than encoding it ahead of action. The temporal relationship is wrong. Governance that follows cognition; that reviews, samples, or self-assesses after the reasoning has occurred; has already ceded the moment where governance matters.
The independence requirement
Governance must be architecturally separate from the agent’s process.
This is not an implementation preference. It is a constitutional requirement that follows directly from the thesis. “Constraint precedes cognition” structurally requires that the constraint evaluation is not performed by the entity being constrained. If the agent evaluates its own boundaries, constraint does not precede cognition, it is cognition. The agent’s reasoning about its authority is part of the same cognitive process that produced the action. There is no separation. There is no gate. There is self-assessment, which is a different thing from enforcement.
The formal precedent is older than autonomous systems. In the 1972 Computer Security Technology Planning Study, J. P. Anderson defined the reference monitor: a mechanism that mediates all access to objects, satisfying three properties:
Complete mediation: the monitor is always invoked; no access occurs without passing through it.
Tamper-proof: the monitor cannot be altered by the entities it governs.
Verifiable: the monitor is small enough to be subject to analysis.
Rushby’s 1981 separation kernel extended Anderson: the governed entity and the governance mechanism run in architecturally separate partitions, operating as if on separate machines. The separation is structural, not procedural. The governed entity cannot access the governance mechanism’s state. The governance mechanism cannot be influenced by the governed entity’s behaviour.
Practitioners building governance for autonomous systems have arrived at the same architecture independently. A process-isolated deterministic gate evaluates every action the agent intends to take. The agent generates a structured intent payload. The gate evaluates it against the authority scope using deterministic logic. The agent and the gate run in separate processes, separate memory spaces. The agent asks for permission. The gate decides. The agent’s runtime can fail catastrophically, and the gate remains untouched.
This is not the only possible implementation. But it demonstrates the structural requirement: the evaluation of authority must be architecturally independent of the exercise of authority. The two functions must not share a process, a runtime, or a decision path. The gate is not the agent’s conscience. It is a separate constitutional mechanism.
Encoded ahead of cognition
The thesis has a precise meaning. Four properties define it.
The authority scope exists before the agent reasons. The authority graph, the composition contracts, the delegation rules, all are defined, deployed, and enforceable before the agent’s cognitive process begins. The agent does not determine its own scope. It operates within a scope that was determined for it. This is not a limitation on the agent’s capability. It is the constitutional framework within which capability is exercised.
The evaluation occurs before execution. Every action passes through an enforcement point that evaluates it against the authority scope before the action proceeds. Not after. Not in parallel. Before. The temporal ordering is non-negotiable. An action that executes before its authority is evaluated is an ungoverned action, regardless of whether the evaluation occurs one millisecond later. The distinction between pre-execution and post-execution governance is not about speed. It is about structural ordering. Enforcement that comes after action is monitoring. Enforcement that comes before action is governance.
The enforcement does not require interpretation. The authority scope is machine-readable. The enforcement point evaluates it deterministically; scope matching, delegation chain verification, composition contract evaluation. The enforcement mechanism does not need to understand the action the way the agent understands its task. It needs to verify that the action falls within a pre-defined scope. This is what makes machine-speed governance possible: the evaluation is structurally simpler than the cognition it constrains. The agent reasons about complex goals. The gate asks a single question: is this action within scope?
The legibility record is a byproduct. When enforcement evaluates before execution, the legibility record: attributable, traceable, interpretable; is produced at the point of evaluation, not reconstructed after the fact. Every evaluation produces a record of what authority was invoked, what scope was checked, and whether the action was permitted. Legibility becomes a structural property of enforcement, not a separate logging system. The three properties from the previous article are satisfied automatically when constraint precedes cognition.
The engineering precedent for this temporal ordering is extensive. In software engineering, Design by Contract requires that preconditions are satisfied before a method executes, the contract is evaluated before the code runs. In cloud infrastructure, Kubernetes admission controllers intercept every request before the object is persisted, the request does not proceed if denied. In functional safety, IEC 61508 requires that safety functions prevent hazardous states rather than detect them; interlocks make unsafe transitions structurally impossible. In security architecture, Zero Trust requires that every access request is evaluated before being granted... never trust, always verify.
None of these are novel claims. Pre-execution constraint evaluation is standard engineering practice in every domain where the consequences of unconstrained action are unacceptable. The thesis applies the same temporal ordering to authority governance: constraint before cognition, evaluation before execution, the gate before the action.
The control-surface band
The architectural concept that makes “constraint precedes cognition” concrete is the control-surface band: the governance evaluation layer that sits between the agent’s reasoning and the system’s execution.
Every action the agent intends to take must pass through the control-surface band before it can execute. The band evaluates the action against the authority scope. If the action crosses a domain boundary, the band evaluates it against the composition contract. If the action involves delegated authority, the band verifies the delegation chain. If the evaluation passes, the action proceeds. If it does not, the action is denied. The denial is not a suggestion. It is structural, the action cannot reach execution without passing through the band.
The control-surface band is where the series’ constitutional architecture becomes operational:
The authority primitive provides the scope against which actions are evaluated. The composition contract provides the rules that govern cross-domain interactions at the band. The legibility properties are produced as outputs of the band’s evaluation. The independence requirement is satisfied by the band’s architectural separation from the agent.
The band operates at machine speed because its evaluation is structurally simpler than the agent’s cognition. The agent reasons about complex tasks, interprets ambiguous goals, generates creative solutions. The band asks a single question: is this action within scope? The answer is deterministic. The evaluation is fast. Governance does not slow the system down. It constrains the system at the speed the system operates.
Anderson’s reference monitor properties apply directly: the band provides complete mediation (every action passes through it), it is tamper-proof (architecturally separate from the agent), and it is verifiable (its logic is deterministic and testable). These properties have been implemented in deployed systems for decades: admission controllers, policy engines, safety interlocks. The control-surface band applies the same architecture to authority governance.
Partial governance is not governance
The thesis is precise: constraint precedes ALL cognition.
A system where most actions pass through the control-surface band and some bypass it is not a mostly-governed system. It is an ungoverned system with a governed centre. The actions that bypass the band: the peripheral cases, the edge interactions, the decisions the designer did not anticipate; are precisely the actions that produce governance failures. Decisions migrate to the periphery. They always do. The ungoverned fraction becomes the governance-relevant fraction.
Monitoring the periphery does not resolve this. Monitoring discovers governance failures after they occur. At machine speed, the gap between the ungoverned action and its discovery widens until the system has already compounded the consequences. The previous article established this: a system with legible domains and illegible seams is a system where every failure migrates to the boundary.
The temptation to govern the core and observe the rest is understandable. It is realistic about implementation difficulty. It is familiar from defence-in-depth thinking. But the thesis demands more. Constraint precedes ALL cognition means that every action, not most, not the core’s, every action, passes through the control-surface band. Actions the band cannot evaluate are not permitted to proceed. Default denial at the governance layer follows the same principle as default denial at the composition seam: an action without explicit authority is an ungoverned action.
This does not mean the control-surface band resolves everything. The architecturally honest position names the limit precisely. Deterministic enforcement handles everything the authority scope covers; the vast majority of actions. The remaining cases, genuine sovereign deadlocks, novel conflicts that no existing authority scope addresses, escalate to human judgment. Not because the architecture failed, but because the architecture correctly identified its own limit. The limit is real. The architecture must name it. But the limit is the point where designed governance reaches genuine novelty, not the point where designed governance stops and observation begins.
The escalation itself is governed. The governance layer identifies the case as beyond its scope, escalates it through a defined mechanism, and records the escalation as a legibility event. The resolution, once made by human judgment, is encoded back into the governance layer. The scope expands. The escalation volume shrinks. Courts do not scale by hiring more judges. They scale by turning precedent into predictable rule.
There is no ungoverned periphery. There is the governed scope and the honest limit. Everything below the limit passes through the band. Everything at the limit escalates through governed channels. The periphery, the space where actions proceed without governance, does not exist in the architecture. That is the thesis.
What comes next
This article has closed the constitutional argument.
Authority is a designed primitive: explicit, scoped, enforceable. It composes through constitutional contracts: conjunction, disjunction, delegation, precedence. It is legible: attributable, traceable, interpretable, verifiable. And it operates at machine speed: through a control-surface band that evaluates every action before execution, architecturally separate from the agent it constrains.
Constraint precedes cognition. This is not a principle to aspire to. It is an engineering requirement. The only architecture that governs at the speed autonomous systems operate is the architecture where governance is already in place before the first decision is made.
But governance that operates at machine speed does not just prevent failure. It produces something the series has not yet named.
Organisations that have solved the governance problem structurally do not just avoid the failure modes Phase I documented. They act faster, because the governance layer adds no latency. With more confidence, because every action is known to be within scope. Across more domains simultaneously, because composition contracts are evaluated at the band, not negotiated at runtime. The constitutional architecture does not constrain capability. It enables it. Capability exercised within designed authority is capability that can be trusted, extended, and composed.
The payoff of constitutional architecture is not compliance. It is decision advantage. The next article names it.
Autonomy was already here.
Hierarchy could not govern it.
Oversight could not contain it.
Boundaries without enforcement could not hold it.
Authority was designed.
It composed.
It became legible.
It was encoded ahead of cognition.
Constraint precedes cognition. The constitutional argument is complete.
What it produces is not.
Next in the series: Decision Advantage


