Authority Composition
When governed systems meet, whose boundary governs?
Authority that cannot compose is authority that cannot scale.
The previous article introduced a first-class primitive: authority as a decision right: explicit, scoped, enforceable, delegable, observable, terminable. The authority graph maps those decision rights across a system. Within a single domain, the primitive governs. Overlap is visible. Gaps are named. Delegation chains are traceable.
But no system of consequence operates within a single authority domain.
The moment two governed systems interact - two supervisory domains, two authority graphs, two independently designed governance structures - a question arises that the primitive alone cannot answer. Both systems are governed. Both enforce boundaries. Both exercise legitimate authority within their scope. And at the point where they meet, neither domain’s governance covers what happens next.
This is not a coordination problem. It is not solved by adding a message bus, a mediator, or a shared orchestrator. It is a sovereignty question: when two legitimate authorities conflict at a shared boundary, whose rules apply?
This article answers that question.
Sovereignty, not scaling
The instinct is to treat composition as a scaling problem. Two systems need to interact, add a coordination layer. Three systems, add an orchestrator. Ten systems, add a platform. The vocabulary is familiar: routing, mediation, sequencing, load balancing. The tools are mature.
None of them address the actual problem.
Coordination manages traffic. It determines what runs, in what order, through what channels. Composition determines whose rules govern when rules conflict. These are different questions with different structural consequences. An orchestrator that resolves a conflict between two authority domains has not coordinated them. It has made itself the governing authority, without being designed as one, without explicit scope, without the six properties the previous article established as non-negotiable. The coordination layer becomes an unaccountable authority by default.
The distinction maps to a pattern older than autonomous systems; Nations do not merge jurisdictions to trade. They establish treaties, frameworks that constrain what is negotiable while preserving the sovereignty of each party. A treaty does not eliminate the difference between legal systems. It defines the terms under which those systems interact without either surrendering its governance.
Federalism operates the same way. The combination of “shared rule and self-rule,” as constitutional theory defines it, allocates authority between levels where neither can unilaterally alter the allocation. The subsidiarity principle determines which level governs based on structural criteria; not negotiated case by case, but defined in advance by the constitutional framework itself. When the European Union acts, it acts only within competences explicitly conferred by member states via treaties. When it does not have explicit authority, it does not act. The composition is constitutional.
This is the register in which authority composition operates. Not middleware. Not message passing. Constitutional design: determining whose rules apply before the interaction occurs.
Four composition primitives
When two authority domains meet, their interaction is governed by one of four structural mechanisms. These are not implementation patterns. They are constitutional primitives; each determines what kind of composition is structurally permissible.
Conjunction. Both authorities must permit the action. Neither gate subordinates. Interaction proceeds only if both domains’ governance allows it.
This is the most conservative composition and the appropriate default when domains are independently sovereign. Practitioners building governance for autonomous systems have already arrived at this pattern: each system maintains its own policy gate, composition becomes gate-to-gate rather than agent-to-agent. Independence first. Composition follows. The action is not evaluated by one domain’s rules and then the other’s. Both evaluations are independent, both must pass, and neither domain defers to the other’s judgment.
In formal policy composition, this is the deny-overrides algorithm: if any policy evaluates to Deny, the combined result is Deny regardless of what other policies permit. The most widely deployed composition primitive in access control, and the most structurally honest. What it sacrifices in speed it gains in governance; no action proceeds without the explicit consent of every sovereign domain involved.
Disjunction. Either authority may independently permit the action. When domains have overlapping but non-conflicting scope and speed matters more than consensus, disjunction allows either domain’s governance to authorise.
This is the permit-overrides algorithm: any Permit result produces Permit. Two monitoring domains both watch the same system. Either can flag an anomaly for investigation. Disjunction is appropriate here: you want either domain’s detection to trigger a response. But if those same domains hold authority over transaction approval, disjunction means either can approve what the other would block. The structural test is precise: disjunction is safe when each domain’s individual governance is sufficient for the action in question. It is dangerous when the action requires the combined judgment of both.
Disjunction without trust is abdication. And the trust is not cultural, it is structural. The composition must define, for each class of interaction where disjunction applies, which domain’s result governs the downstream consequences when the two domains disagree. Without that definition, disjunction does not compose authority. It dissolves it.
Delegation. One authority explicitly grants a scoped portion of its decision rights to a component in another domain. Cross-domain delegation carries the same requirements as within-domain delegation: explicit scope, enforceable conditions, termination. But adds a provenance challenge. The receiving domain must be able to verify the delegation chain back to its source. Authority that arrives without verifiable provenance is indistinguishable from authority that was never granted.
In capability-based security, this is the principle that enables robust composition of independently-developed components: authority is held as unforgeable references rather than ambient permissions. Delegation transfers a capability. Attenuation creates a less-powerful version. Confinement prevents leakage beyond the intended scope. The structural discipline is the same at the authority level: what is delegated, to whom, under what constraints, and whether the delegate may further delegate must be explicit before the delegation occurs.
Precedence. A defined ordering that resolves conflicts when authorities overlap and neither conjunction nor disjunction applies. Precedence is not hierarchy. It does not make one domain permanently subordinate. It is a pre-agreed resolution rule for a specific class of conflict.
Precedence governs the cases where conjunction would produce deadlock and disjunction would produce incoherence. Two authority domains disagree about whether an action should proceed. Conjunction blocks it. Disjunction permits it. Neither result reflects the governance the composed system actually requires. Precedence resolves the disagreement by applying a pre-agreed rule: for this class of conflict, this domain’s authority governs.
The critical word is “class.” Precedence is not a blanket ordering. It applies to specific interaction types defined in the composition contract. Domain A may have precedence over transaction limits while Domain B has precedence over data handling. The ordering is structural, not political, determined by which domain’s governance is most relevant to the specific conflict, not by which domain is more powerful.
Constitutional law provides the structural model. The preemption doctrine determines when higher authority displaces lower, not universally, but for specific conflict types. Express preemption applies when the higher authority explicitly restricts the lower. Implied preemption applies when lower authority’s rules contradict higher or when higher authority occupies an entire regulatory field. In both cases, the resolution is defined in advance by the constitutional framework, not negotiated at the point of collision. And courts sometimes favour local authority when significant interests vary by locality. Precedence is contextual, not absolute.
Each primitive carries a structural consequence. Conjunction prevents action without consensus. Disjunction enables speed at the cost of unanimity. Delegation extends authority across boundaries with explicit terms. Precedence resolves conflicts through pre-agreed ordering. The choice between them is not a technical configuration. It is a constitutional decision about what kind of governance the composed system provides.
What fails at the seam
The failure modes of composition without rules are not hypothetical. They are the structural consequence of authority domains interacting without a defined composition primitive.
Context escalation. Information crosses a domain boundary and is interpreted as authority. An agent in one domain retrieves output from another domain’s process and treats it as authorisation for a transaction that neither domain independently approved. Context propagation becomes permission escalation, not because either domain’s governance failed, but because the seam between them converts information into authority without invoking either domain’s governance.
This pattern surfaces in regulated environments with particular clarity. When authorisation boundaries sit between agents, context that flows across those boundaries carries implicit authority the sending domain never granted. The receiving agent does not forge a permission. It interprets a context. The interpretation has the same structural effect as a forged permission: action proceeds without authority, but it is invisible to both domains’ governance because it occurs at the seam, in the space neither domain governs.
In capability-based security, this is the confused deputy problem: legitimate authority is misdirected because the composition lacks explicit scoping. A program acting on behalf of two principals cannot distinguish which authority justifies which action. The confusion is not cognitive. It is structural, the composition did not define whose authority applied.
Invariant collapse. Each domain preserves its own governance properties. Composition violates properties that exist only at the interaction level. Two locally sound authority models meet, and the combination permits a state that neither model permits alone. Local governance holds. Global coherence fails.
The requirement this failure mode reveals is mutual legibility of invariants. Each domain must be able to verify that composition preserves its essential properties. When invariants are not mutually legible across domain seams, composition becomes a backdoor, a path through which the composed system reaches states that each domain’s governance was designed to prevent.
Provenance loss. Delegation chains that cross domain boundaries lose traceability. A decision is made in the composed system, but no single authority graph can reconstruct who authorised it. Accountability becomes forensic; reconstructed after the fact rather than traceable by design. The composed system exercises authority. The provenance of that authority is lost at the seam.
These are not edge cases. They are the default outcome when governed systems interact without composition rules. And they share a structural root: the space between domains, the seam, is ungoverned. Each domain’s governance extends to its boundary. Neither extends into the gap.
The composition contract
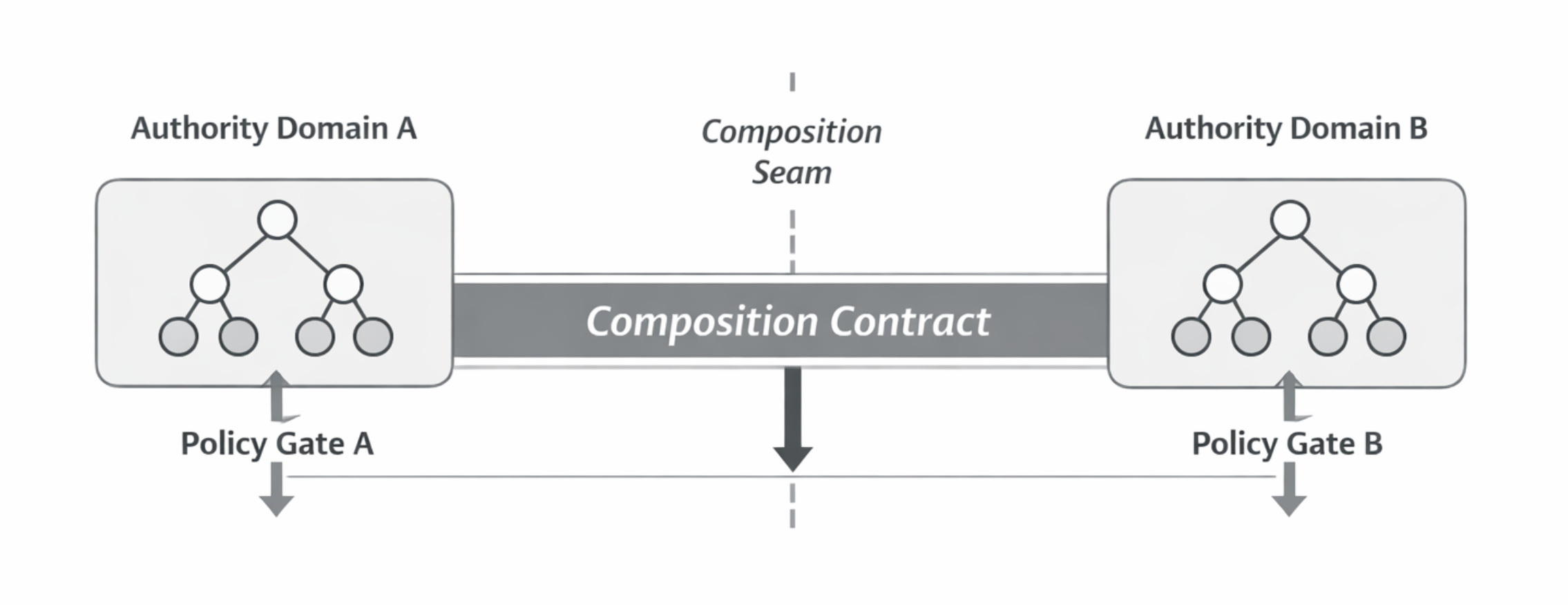
The sovereignty question has a structural answer: the composition contract. When two authority domains compose, they agree, in advance, not at runtime, on a defined set of terms.
Which composition primitive governs. Conjunction, disjunction, delegation, or precedence. The choice is explicit for each class of interaction. A single composition contract may use different primitives for different interaction types; conjunction for actions that affect both domains’ core invariants, delegation for routine cross-domain operations, precedence for conflict resolution in a specific scope.
What invariants must survive. Not all invariants from both domains, that would make composition impossible. A manageable, explicit set of properties that the composed system must preserve. The choice of which invariants survive composition is itself a governance decision. It defines what the composed system guarantees and what it does not.
How conflicts are resolved. When composition produces a state that the contract did not anticipate, what happens? The contract must define a resolution mechanism: arbitration, escalation, or default. The mechanism is agreed before the interaction, not improvised during it.
What remains sovereign. Which decisions each domain retains exclusively and which are subject to the composition contract. Sovereignty that is not explicitly preserved is sovereignty that has been implicitly ceded. The composition contract must name what is non-negotiable.
Return to the refund-fraud scenario from the previous article, now at the composition level. The payment domain governs transaction execution: refund approval, amount limits, account validation. The fraud domain governs risk evaluation: pattern detection, flag escalation, hold authority. When a customer requests a refund on a flagged transaction, the two domains must compose.
The composition contract specifies: conjunction governs any action that both approves a payment and overrides a fraud flag; neither domain can unilaterally resolve this conflict. The invariant that must survive: no flagged transaction is refunded without the fraud domain’s explicit evaluation completing. Conflict resolution: when conjunction produces denial (fraud blocks, payment approves), the interaction escalates to an arbitration process defined in the contract, not to whichever agent acted first. What remains sovereign: the fraud domain retains exclusive authority over flag status. The payment domain retains exclusive authority over account limits. Neither cedes these decisions to the composition.
Without this contract, the previous article showed what happens: the refund is issued, the fraud flag is raised, no arbitration exists. With the contract, the same interaction, the same agents, the same capabilities, but the relationship between their authorities is constitutional rather than accidental.
The composition contract is not a runtime negotiation. It is a constitutional instrument; defined before the domains interact, enforceable at the boundary, legible to both parties. The treaty analogy completes here. Choice-of-law principles in international commerce formalise this exactly: parties pre-agree on which sovereign legal framework governs their interaction, may select different laws for different portions, and preserve each sovereign’s overriding mandatory rules. The composition contract is the treaty between authority domains.
This is where the emergent-order position must be addressed directly.
The objection runs: designed authority bottlenecks everything at human foresight. Pre-calculating authorised concessions breaks down at scale. Agents should price collisions through emergent value exchange in real time. The composition contract is sophisticated clockwork: rigid, brittle, incapable of handling novelty.
The objection has intellectual depth. Hayek argued in 1945 “The Use of Knowledge in Society” that relevant knowledge “never exists in concentrated or integrated form” and that the price system coordinates dispersed knowledge without central direction; “by a kind of symbol, only the most essential information is passed on.” If emergent coordination outperforms designed coordination for economic activity, why not for authority composition?
Because Hayek’s own later work answered the question.
This is not an incidental concession. In Law, Legislation and Liberty, Hayek argued explicitly that the spontaneous order of the market presupposes “rules of just conduct”: rules that are themselves the product of deliberate institutional design. The price system is not an alternative to designed structure. It is an achievement of designed structure; one that works precisely because the constitutional framework beneath it constrains what market participants can and cannot do. Property rights define what can be traded. Contract enforcement defines what agreements are binding. Courts resolve disputes that the existing framework does not anticipate. Remove any of these and the market does not become a freer market. It ceases to be a market.
The strongest argument for emergent coordination is, at its foundation, an argument for emergent coordination within constitutional structure. It is not an argument against constitutional structure. The composition contract is not the opposite of spontaneous order. It is its precondition.
Mechanism design, the field that earned Hurwicz, Maskin, and Myerson the Nobel Prize in Economics, formalises this from the other direction. When individually rational strategies produce collectively suboptimal outcomes, the response is not better individual reasoning. It is institutional redesign: changing the rules of interaction so that rational behaviour produces coherent results. Mechanism design inverts the question. Instead of predicting what outcomes emerge from given rules, it asks what rules produce desired outcomes.
The emergent-order position is the pre-mechanism-design position. It hopes that composition produces governance without designing for it. The evidence from social norms research is against it. When competing normative frameworks meet without a composition rule, each participant supports the rule that favours them most. Observed breaches erode compliance in others. Locally rational behaviour produces globally incoherent outcomes… not because the participants are irrational, but because the interaction lacks designed structure.
Intelligence amplifies structure. If structure is absent at the composition seam, intelligence amplifies the incoherence.
Residual authority defaults to denial
When a composition contract does not address a particular interaction: when two domains encounter a case their composition rules did not anticipate - the default is denial.
No action proceeds at the composition seam without explicit authority. An uncomposed interaction is an ungoverned interaction. The system must treat it as such.
This is the constitutional counterpart to the principle established in the previous article: ungoverned components are unacceptable. At the composition level: an interaction between governed domains that falls outside the composition contract is an ungoverned interaction. The structural response is the same: default to denial.
Zero trust architecture codifies this as a first principle: no implicit trust granted based on location or identity. Every access request requires explicit authorisation. The EU’s principle of conferral codifies it constitutionally: the supranational institution acts only within competences explicitly conferred. Any action lacking treaty authorisation falls outside legitimate authority.
Default denial is not brittleness. It is honest governance. A system that permits uncomposed interactions is a system that has accepted governance gaps at the most consequential boundary; the point where independently governed systems meet.
The maturation path follows from the default. Denied interactions at the composition seam surface genuine gaps in the composition contract. Those gaps are resolved through judgment at the sovereign boundary, the one per cent of interactions where the architecture correctly identifies that no existing rule applies. The resolution is encoded back into the contract. The composition rules thicken over time.
This is how legal systems mature. Not every principle essential to effective governance can or should be cast immediately into the mold of a general rule. Case-by-case adjudication resolves what the existing framework does not cover. Precedent constrains future resolutions. The doctrine of stare decisis (a legal term in Latin for: standing by things decided) ensures that the same conflict produces the same resolution. Distinguishing narrows earlier holdings when novel facts appear. The treaty layer thickens. The escalation volume shrinks.
Courts do not scale by hiring more judges. They scale by turning precedent into predictable rule.
The composition contract is not designed once and frozen. It begins with fundamental rules and matures through accumulated resolutions. The maturation is itself governed: not every resolution generalises, and the encoding requires the same structural discipline as the original design.
What comes next
This article has established that authority composition is a sovereignty question, not a scaling problem. Four composition primitives: conjunction, disjunction, delegation, precedence, determine what kinds of composition are structurally permissible. The composition contract defines the terms under which independently governed domains interact. Residual authority defaults to denial.
But governance that composes is not yet governance that is governed.
Authority that composes across domain boundaries without being legible; without being traceable through the composition seam, attributable to a specific authority, interpretable in terms of the scope that permitted it, is authority that cannot be audited. And authority that cannot be audited cannot be trusted at scale.
The next article examines what it means for composed authority to be legible. Not logged. Not monitored. Legible: readable by a human who needs to understand what happened, whose authority governed, and whether the composition contract was honoured.
Authority was designed.
It was made explicit, scoped, enforceable.
It composed, across boundaries, between sovereigns, through contracts defined before the interaction began.
The question is no longer whether governance scales.
It is whether governance can be read.
Next in the series: Legibility as Structural Requirement



Aaron, framing this as a question of sovereignty rather than scaling is the exact paradigm shift the industry is missing. The 'Treaty' metaphor is flawless.
To touch on Michael's comment below—this actually doesn't fix the reliability problem with LLMs. And that is the beauty of it. It accepts that stochastic LLMs will always be inherently unreliable, and instead builds a deterministic boundary (a treaty line) around them to contain the blast radius.
When we were mapping the architecture for multi-agent governance, we hit this exact 'seam' problem. We found that you cannot coordinate competing sovereign agents inside a probabilistic space. The 'Composition Contract' you describe must be anchored to a process-isolated deterministic gate, operating on a strict 'fail-closed' (default denial) basis.
If Domain A and Domain B meet, their interaction isn't negotiated by their respective LLMs; it is verified by their respective cryptographic gates against a hashed contract.
You are laying out the precise constitutional physics for the agentic economy. Highly anticipating the 'Legibility' piece—because if the composition contract isn't anchored to a non-repudiable, tamper-evident substrate, the treaty is just written in pencil.
interesting fixes the reliability problem with LLMs